Robust Enterprise Network Security
Your network is the backbone of your digital operations, and keeping it secure is our highest priority. Multiview offers comprehensive network security solutions that safeguard your data across cloud, on-premise, and hybrid environments. We specialize in building "defense-in-depth" strategies that protect your infrastructure from unauthorized access and lateral threat movement.
For years, Multiview has helped businesses navigate the complexities of modern connectivity. By leveraging AI-driven traffic analysis and vendor-neutral security intelligence, we deploy scalable firewall architectures and encrypted tunnels that provide long-term resilience against advanced persistent threats (APTs) and automated exploits.
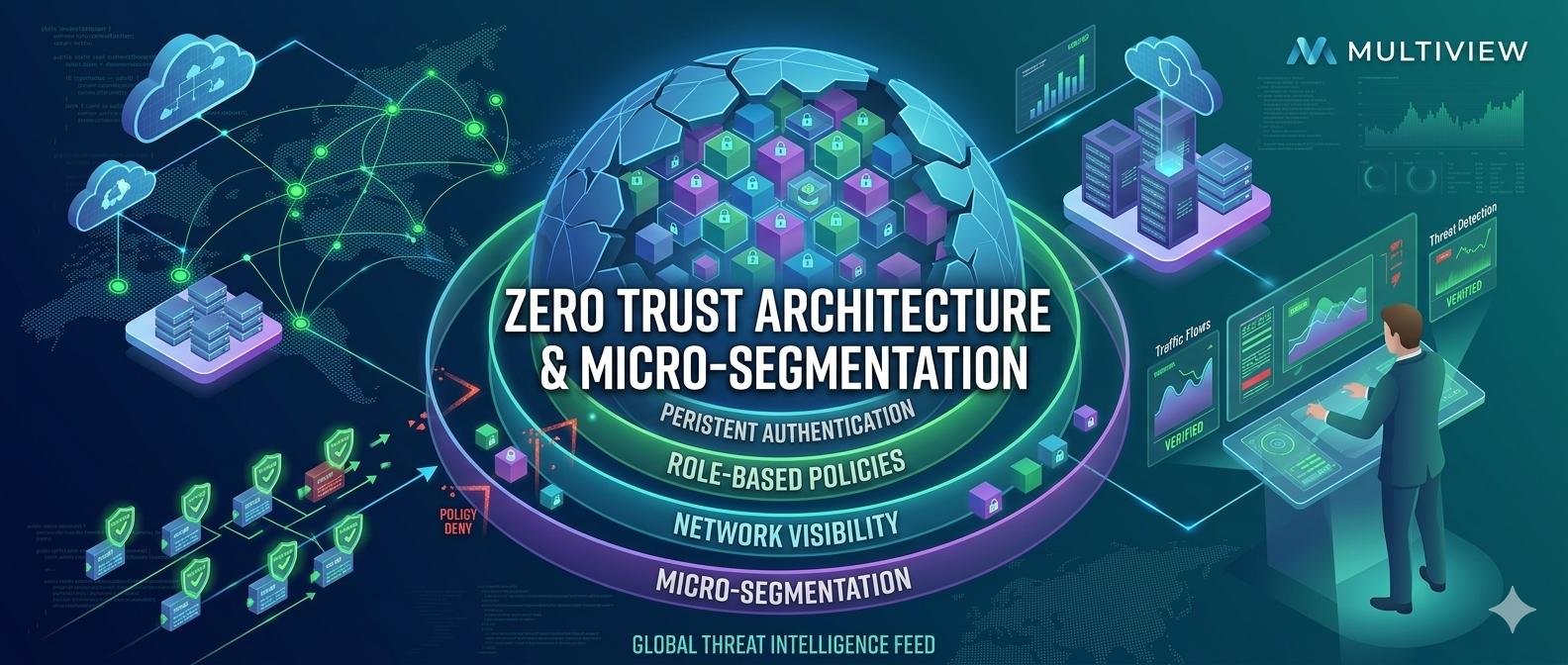
Zero Trust Architecture & Micro-segmentation
Our "multiview" approach moves beyond traditional perimeters. We implement Zero Trust frameworks where every user and device must be continuously verified. By using micro-segmentation, we isolate critical workloads, ensuring that even if one part of your network is compromised, the rest remains impenetrable.
Multiview’s technical refreshment programs ensure your network hardware and software are always ahead of the curve. By integrating real-time threat hunting and automated patching, we deliver high-performing networks that are inherently secure, allowing your team to work from anywhere with total confidence.
Core Network Capabilities
Our network engineering teams focus on five critical pillars to ensure your infrastructure exceeds global security standards:
- Next-Gen Firewalls (NGFW): Deep packet inspection and application-level traffic filtering.
- Managed VPN & SD-WAN: Secure, encrypted connectivity for remote offices and distributed workforces.
- Intrusion Prevention (IPS/IDS): Real-time detection and blocking of malicious network signatures.
- Network Access Control (NAC): Dynamic policy enforcement for every device entering your ecosystem.
- Infrastructure Hardening: Securing routers, switches, and cloud gateways against configuration drift.